This is some text inside of a div block.
SOC 2 Hub
SOC 2, sorted. Best practices, smart workflows, and everything GRC pros need to stay ready.

What's New?
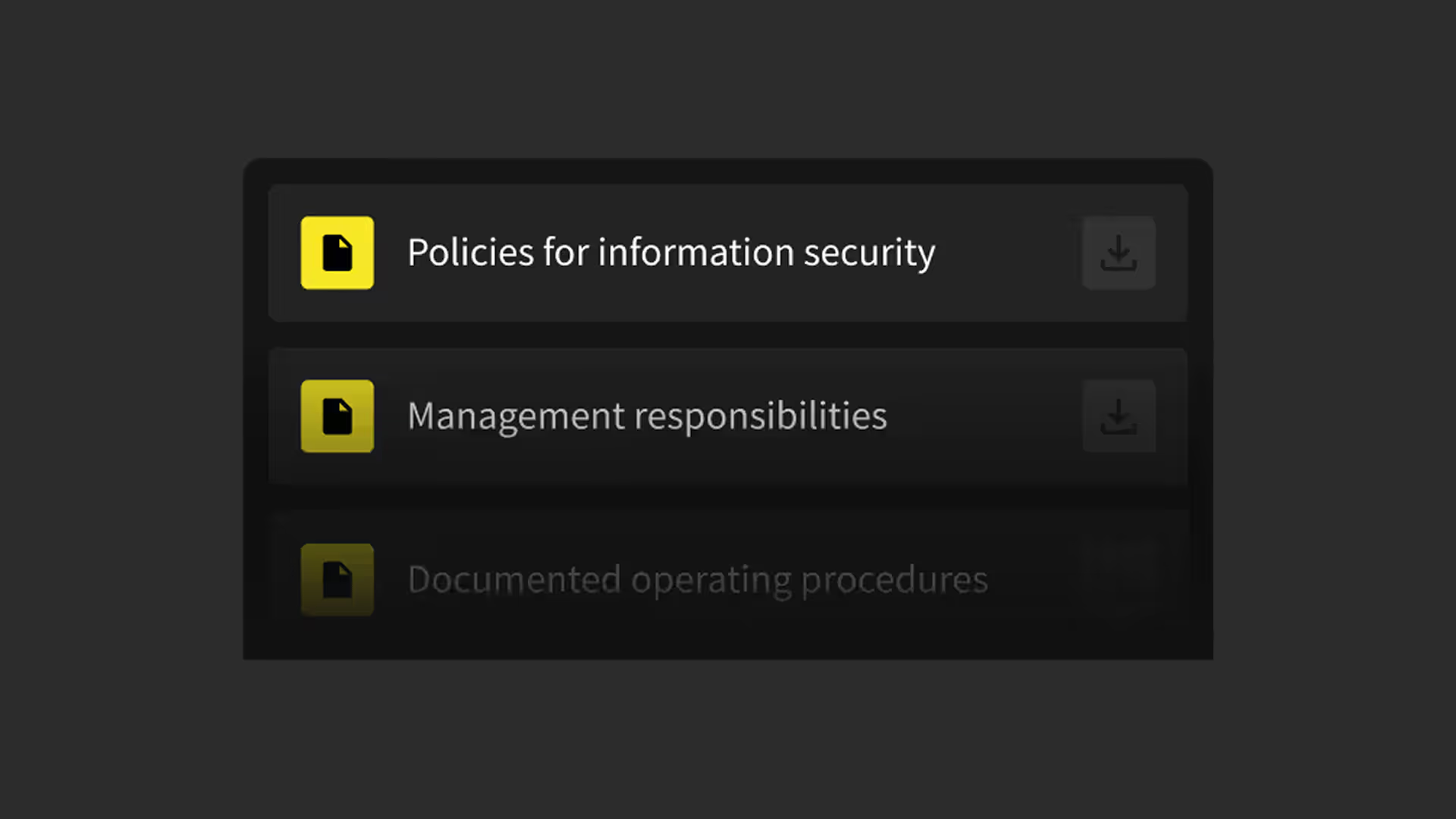
Getting Started
All the resources you need to get going with SOC 2 compliance.
Preparing for Your Audit
Checklists, guides, and templates to help you smash your SOC 2 audit.
Automating and Staying Compliant
Smart workflows and tools to keep you SOC 2 audit-ready.
SOC 2 Essentials
Key links for SOC 2 basics, reports, and requirements.
Your Compliance Newsletter
Stay ahead with the latest expert insights, news, and updates on compliance.











.jpg)
%20(1).png)